This article discusses how to pull browser history from a remote computer running Microsoft Windows.
If trying to manually copy browser history files then there are a number of potential issues to be aware of:
- If Remote Desktop Protocol (RDP) is used to manually copy the browser history files, and someone else is using the remote computer then they will be logged off.
- If a web browser is open on the remote computer then some of the browser history files will be locked, and therefore cannot be easily copied.
- It may be necessary to copy the history files for multiple web browsers and multiple profiles per web browser. Therefore, the number of different files to copy can easily get quite complicated.
To solve these issues we developed a free tool, Browser History Capturer (BHC).
BHC will capture internet history from the following web browsers:
- Chrome
- Edge
- Firefox
- Internet Explorer
The data captured includes:
- Bookmarks
- Browser Settings
- Cached Files
- Cookies
- Downloads
- Favicons
- Form History
- Saved Logins
- Searches
- Session Data
- Site Settings
- Site Storage
- Website Visits
BHC is capable of copying browser history files that are locked by an open web browser. It is also possible to execute BHC remotely using a tool such as PsExec or Powershell. The following guide describes the command line arguments which can be used:
BHC Command Line Guide
We also offer a completely automated solution for pulling browser history remotely within our professional tool, Browser History Examiner (BHE).
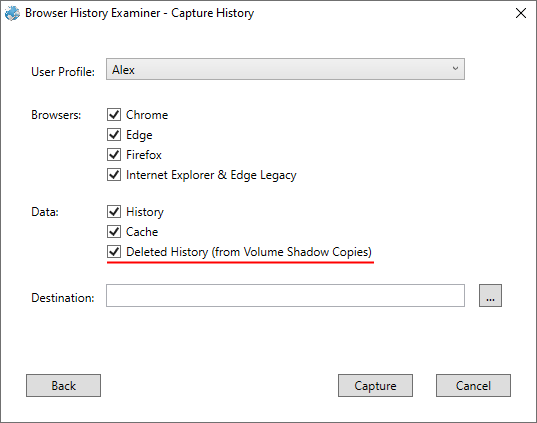
Within BHE you can simply enter the remote computer name or IP address and the credentials for a local/domain admin account, and BHE will automatically pull the internet history from the remote computer back to your computer where BHE is running.
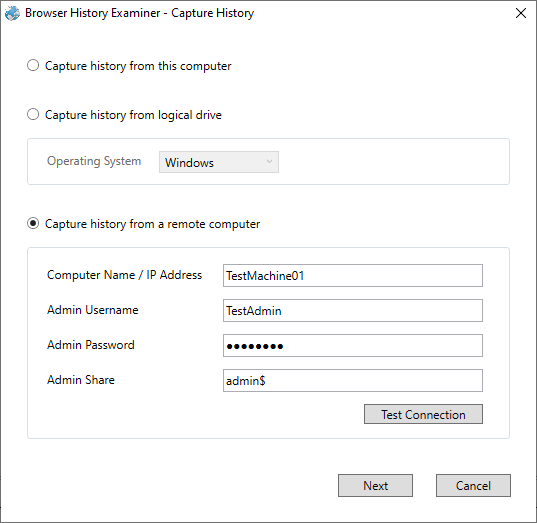
No installation is required on the remote computer and the remote user is not notified when data is captured, making it ideal for ad-hoc and targetted investigations in addition to investigations that need to be carried out discretely.
There is also an option for recovering deleted browser history from the remote computer, which is achieved by processing historical data stored within Volume Shadow Copies on the remote computer.
The remote capture feature within BHE can be used from the trial version without the need to purchase a license.